abstraction
For our purposes, it’s the removal of all unnecessary details, leaving only what’s required for operation.
AC
Alternating current (which is also alternating voltage). This is how power is delivered to homes and factories.
accelerator
A circuit, usually done with hardware instead of software, that can perform some task faster than a processor can. Instead of the processor handling the task itself, it offloads the work to the accelerator, and the accelerator sends the answer (whatever that means for the task) back to the processor.
accelerometer
A sensor that measures acceleration and deceleration.
access point
For wireless network connections like WiFi, this is a router that takes your wireless signal and either connects it to other wireless signals or to a wired signal — say, for going to the cloud.
actuator
A way of controlling some device electronically. It might turn the device on or off or change a setting or property or do any other thing that the device is capable of.
algorithm
A way of calculating something, typically as a step-by-step recipe. A familiar one to all of us is how we do long division on paper: that’s an algorithm. Algorithms abound in the IoT.
alliance
A group of companies working together (in an anti-trust fashion) to promote a particular protocol or set of protocols. They’re like a standards body, but they don’t have the official imprimatur of a standards body.
analytics
Refers to rummaging though lots of data to learn things. This would be done by an IoT device or service provider. For instance, looking at what time of day a gadget gets used most, or seeing if any devices have failed.
anonymize
Taking data that originated from an individual IoT device user and stripping off any parts of the data that can tie the data to that individual. The data then becomes anonymous.
anti-trust
Refers to laws preventing competing companies from anti-competitive behavior.
application programming interface
Commands or functions that let a programmer control some other program or object or thing, or get data from some object, without knowing the details of how it works.
artificial intelligence
A broad term for technology that acts more human-like than a typical machine, especially when it comes to “thinking.” Machine learning is one approach to AI.
artificial neural network
A type of neural network that’s loosely inspired by biological neurons, but operates very differently.
ASCII
An older way of representing characters (letters, numbers, and punctation) in computers. It could handle only characters relevant to English and languages using those characters. It has mostly been replaced by Unicode, which can represent all the world’s characters.
assembler
A software development tool that takes a low-level assembly-language program (source code) and translates it into a machine-language program (object code).
assembly language
This is a more human-readable version of machine language. It’s still low-level, but it uses text instead of 1s and 0s.
asymmetric key
A way of encrypting data that uses one key for encrypting and another for decrypting.
attack surface
Industry jargon for a way to break into a device or network or anything.
attestation
A security operation that involves “inspecting” software (and perhaps also data) to check whether anything has been altered.
authentication
This is the act of proving to some other entity that you are truly who you are representing yourself to be. That is, you’re not pretending to be someone else. “You,” of course, means a computer or IoT device or any other entity trying to make a network connection with another computer or device.
authorization
The process of deciding what privileges – if any – someone gets on a network, server, or other asset.
band
A specific range of frequencies. Usually smaller and more specific than what’s referred to by spectrum. You would refer to the AM radio band, not the AM radio spectrum. That’s where CB – Citizens’ Band – comes from.
bare metal
Describes a system that has no OS. Software runs directly on the hardware.
best practices
A term referring to ways of doing things (business, technology, etc.) that an industry generally views as the best way to do things. Best practices take time to establish, and they usually relate to basic principles, leaving lots of options on how to do specific things.
binary
A base-2 counting system (rather than the base-10 system we usually use). Digits can be 0 or 1.
bit
The smallest unit of information. It is a shortened form of “binary digit.” Since it’s binary, it can have only two values — typically 0 and 1.
bit cell
A cell that stores a single bit within a memory. (Some can store more than one bit.) It connects a word line to a bit line. The bit cell can either conduct or not conduct current; those are the two states of the memory cell.
bit line
A line in memory that can detect whether a bit cell conducts current. This is how the memory is read. The bit lines and word lines are orthogonal to each other, making an array of the bit cells that connect them.
blockchain
An electronic ledger system where all entries are confirmed by some decentralized mechanism, like voting, and cryptographically attested so that, if someone changes one entry anywhere, it will be obvious.
blocking
In the context of a thread, refers to execution that may have to wait for a result to come back before it can proceed. While waiting, it’s said to be blocked.
boot code
Software that loads and runs when a device first powers up.
brick
Used as a verb, indicates taking a device that performs some function and eliminating or disabling that function. It’s considered no better than a brick at that point.
broker
A server that manages published data and subscribers to that data as part of a publish-and-subscribe setup.
bus
A way of connecting the components of a computing system where the components all share the same wires, but a controller makes sure that only one device can put its signals on the wires at a time.
bus protocol
The “rules of the road” for a specific bus. Determines how a bus controller decides who gets access to the bus when.
business rules
Rules that say, “if this happens, then do that.” Like, “if the ground is too dry, then turn on the sprinkler.”
byte
A byte is 8 bits.
C
A programming language that gives low-level control of all the details.
cache
A place to park data coming from slow memory so that you can access it quickly. It’s built with SRAM memory, but it’s organized so that you can figure out which parts haven’t been used in a while so that they can be replaced with new cached items. Also, if you make a change to cached data, that change has to make its way back into the original slow storage.
cache hit
Refers to the situation where you need memory data that’s already in the cache.
cache miss
Refers to the situation where you need memory data that’s not already in the cache, so you first need to load it from slower memory into the cache.
capacitance
Capacitance is the ability of an electron or hole to “feel” other electrons or holes on the other side of a small gap. The gap prevents actual current from flowing, but, if small enough, electrons and holes can pile up on either side of the gap. Specific devices that make use of this are called capacitors.
certificate
A digital document that certifies, more or less, that someone is who they say it is. It’s issued by a certificate authority.
certificate authority
A trusted organization that issues security certificates.
chip
An electronic device made on a piece of silicon. These days, it could also involve a mechanical chip, but, to the outside world, everything looks electronic. The chip is usually in some kind of package; that package might contain multiple chips. “Integrated circuit,” and “IC” mean the same thing, but refer only to electronic chips, not mechanical chips.
CIoT
Consumer Internet of Things. IoT gadgetry designed for home and personal use.
CISC
Complex Instruction Set Computer; a kind of processor architecture that may have many, many instructions that are complicated and specialized. This term contrasts with RISC.
CMOS
A way of connecting MOS (metal-oxide-semiconductor) transistors into a switch that conducts no current when sitting idle.
CNN
A type of artificial neural network specifically used for machine-vision applications.
CoAP
A communications protocol that uses the RESTful approach for small systems such as those used for the IoT.
collusion
Competing companies getting together to reduce competition by agreeing on pricing or splitting up territories or in other ways arranging not to compete. This kind of collusion is, at least in the US, illegal (although enforcement isn’t guaranteed).
compass
In its electronic version, a magnetometer that has its reading compensated by a tilt meter (done by an accelerometer).
compiler
A software development tool that takes a high-level program (source code) and translates it into a low-level machine-language program (object code).
computer farm
A collection of computers that are interconnected so that they can share and distribute work. For our purposes, it’s the same as a data center, but the focus is on the collection of computers.
conductance
The literal opposite of resistance. Rather than how hard is it to push the flow through, it looks at how easy it is. Measured in mhos.
conductor
A material through which electricity can flow. Metals are a good, familiar example.
connection
This refers to some kind of electrical connection. It might be through a network cable, a cable connection, a wireless connection, or a phone – just to name some options. The connection might be to the internet or to some other local device.
container
A way of separating applications running on the same server. It’s lighter-weight than a full virtual machine.
context switch
Refers to a CPU changing from one thread to another, with all of the related information from one thread being stored and replaced by the same type of information for the new thread.
convention
An agreement on some decision that could be made several ways. For example, given a single bit, you could decide that 1 means “true” and 0 means “false,” or you could decide the opposite. Similar in spirit to a protocol, but protocols usually deal with how something is done — a step-by-step process, for example.
core
This can have more than one meaning.
When discussing networks, the core is the heart of the network where much of the traffic (or at least that part that has to go a long ways to its destination) moves. This is in contrast to the edge — the outer part of the network where devices like computers and printers get connected.
When discussing computers, you can think of it as the same as a CPU.
CPU
Stands for “central processing unit.” Basically, it’s a microprocessor – the main one in the computer. Things get a bit more complicated because, these days, there may be more than one microprocessor. But you can safely think of all of them together as the CPU.
cryptocurrency
A form of artificial currency that uses blockchain technology. Bitcoin and Ethereum are better-known examples.
current
The amount of electrical flow. Measured in amperes or amps (A).
data analyst
Someone whose job it is to go through accumulated data to learn something from the data.
data center
A collection of computers that are interconnected so that they can share and distribute work. For our purposes, it’s the same as a computer farm, but the focus is on its application for processing data.
database
A structured way of storing data and relating different pieces of data to each other. (Like, which address belongs to which person.) There are “query” languages, the best-known of which is SQL, that let you enter data into the database, change data that’s already in the database, and retrieve data from the database.
DC
Direct current (which has constant voltage). This is what electronics require as an energy source.
dead reckoning
The process of determining your position through a series of speed and heading calculations. Small errors can accumulate if your measurements and those calculations aren’t accurate enough.
decimal
The base-10 counting system that we usually use. Digits can go from 0 to 9.
decommissioning
This is the process of “unregistering” an IoT device that you’re not going to use anymore. It keeps someone else from using it (if it’s lost or stolen).
degree of freedom
A setting or property that can be adjusted independently without affecting any other setting. With movement, there are three straight-line degrees of freedom: forward/backward, up/down, and left/right.
demodulation
This generically refers to how data can be received on some physical medium – like a wire or a radio signal. Voltages might be moving up and down, or the frequency of some periodic signal might be changing. There are lots of ways of “coding” data so that it can travel across the medium. It’s a really low-level detail; most of us don’t need to know any of the fine print. The opposite of demodulation is modulation , and a piece of network equipment that does both (modulation for sending, demodulation for receiving) is called a “modem.”
dependency
In a computer program, refers to the situation where one piece of the program depends on the result of some other part of the program. If we calculate 1+1, then there’s no dependency. If we calculate a+b, then our result depends on whatever prior calculations produce a and b.
deposition
A means by which materials can be added to a silicon wafer.
detection
In the context of machine vision, a task that identifies the particular type of object in the image – chair, person, cat, etc.
digest
The result of a hashing operation.
digital signal processing
A processor optimized for handling computations involving digital representations of analog signals.
digital signature
An encrypted digest that can be appended to a message or sent separately from the message.
digital twin
A virtual version of a specific piece of hardware – airplane engine, car, etc. – that behaves like and mirrors the true hardware version, keeping in synch with it. Such models can often be used to predict things like wear-out before they happen.
diode
An electrical component that allows current in one direction but blocks it in the other direction.
distributed computing
A way of breaking up calculations and letting more than one computer work on different pieces at the same time in order to speed up the solution.
DRAM
Stands for “dynamic random access memory.” This is temporary working memory in a computer. When the
DTLS
Datagram transport-layer security. This is a security protocol analogous to TLS. TLS is used with TCP; DTLS is used with UDP (which sends so-called datagrams). Some version of this or TLS should be in IoT devices.
dynamic power
The rate of energy consumption of a circuit while it’s switching — that is, while computing or otherwise doing work.
ecosystem
A group of related businesses that agree to work together, typically through a somewhat formal organization that may have a brand name. If something like that existed, for, say, produce sold in a grocery store, then the ecosystem might include select farmers, distributors, transportation companies, and grocery stores.
edge
This term is slightly confusing because, in different contexts, in means slightly different things. In general, when talking about networks, it refers to that part of the network where devices (computers, printers, etc.) are connected. That’s in contrast to the core, which is the middle of the network where lots of traffic gets moved around.
electron
A fundamental particle found outside atoms. It carries a negative charge. It can move easily in a conducting material, which gives rise to electrical current.
emulation
Refers to one kind of system that can behave as if it were another kind. A good example is a Macintosh, which, by itself, works very different from an Intel/Microsoft-based PC. But a Mac can pretend to be a PC by emulating how a PC works.
emulator
In the context of chip design, a specialized computer that can implement a model of a chip design for testing that design thoroughly prior to building real chips.
encapsulation
When the details of how something works is buried inside the code for an object in a way that lets some other programmer use it without knowing those details, we say that the details have been encapsulated.
encryption
Encryption refers to encoding and decoding (or encrypting and decrypting) data so that it can’t be read unless you have the right key. It’s critical for good security.
energy harvesting
Technology that can grab energy from the environment for local use with low-power devices.
etching
A means by which materials can be removed from a silicon wafer.
Ethernet
A very common Layer 1 and 2 standard for wired network connections.
firmware
Software that is stored on a device itself. Regular computers have very little firmware, since software mostly comes from a hard drive or some other storage. But on IoT devices, much of the software may be firmware.
flash memory
A type of memory that can retain its contents even with the power off. Thumb drives use flash memory.
fragmentation
This can have two different contexts.
For message packets: When the contents of a message are too long for a packet, then the message is fragmented into multiple packets for sending, and those fragments are reassembled on the receiving end of the message.
For memory: A situation where free memory is broken up into small pieces throughout the memory rather than accumulated at one spot. This makes it harder to allocate the free memory, since the small pieces may be too small for a new allocation request.
frequency
The rate of change of a signal, specified in hertz, or cycles per second.
FUD
Fear, Uncertainty, and Doubt. This is a sales tactic used to confuse someone about the competition. The information may or may not be true, but using FUD is often seen as a somewhat desperate way to get a sale.
function
A small portion of a program that’s set aside and given a name. It helps isolate key code in an easy-to-understand way, and it makes changes easier and less error prone. It’s a really important way to make programs easier to understand. May also be called a subroutine.
garbage collection
The process of defragmenting memory by moving multiple free “holes” in memory together so that they can be allocated more effectively.
gateway
A piece of electronic network equipment that takes a local network and gives it access to the internet. Your cable modem, for instance, might act as a gateway.
GDPR
General Data Protection Regulation. A set of privacy rules governing how EU residents’ personal data must be handled.
GPS
Global Positioning System. A satellite system that sends signals to earth. GPS receivers can get those and figure out where on the earth you are. This is specifically a US-based system, an example of the more generic term “GNSS.”
graphics processing unit
A processor optimized for rendering images and video on a display.
gyroscope
A sensor that detects when it changes direction.
hack
This can mean a couple things. A quick-and-dirty (but not elegant) trick to get something done is a hack. A computer security break-in is also a hack (because inelegant tricks are used to break in). It can be a noun or a verb (“he hacked my computer”).
hacker
A misused, but common term for an unauthorized person trying to break into a device or network. Originally, in this context, “hackers” referred to the good guys (or “white hats”), while “crackers” were the bad guys (black hats).
hard drive
A type of persistent (non-volatile) memory built from rotating platters and “read heads” that sense the data on the platters.
hardware
In this context, “hardware” refers to functions in an IoT device that are built into a silicon chip or some other dedicated component. It’s distinct from “software,” which refers to instructions running on a processor.
hardware root of trust
A chip of some sort that stores security artifacts like keys and certificates. It can perform the security operations itself so that those artifacts never have to (and can never) leave the chip.
hash
A way to combine the contents of a message to generate a value that is almost unique to that message.
heap memory
A block of working memory reserved for use by programs as they request an allocation. The programs request and release memory from the heap as they go, and where specific data will end up in the heap is unpredictable.
hertz
The unit used for frequencies. It’s abbreviated Hz. Equivalent to cycles per second. A periodic signal that completes a cycle in one second is said to have a frequency of 1 hertz, or 1 Hz.
hertz
A measure of frequency, or how often something repetitive can happen in a given time. Specifically, it means one cycle per second.
hexadecimal
A base-16 counting system (rather than the base-10 system we usually use). Digits can go from 0 to 9 and then A, B, C, D, E, and F.
hole
In a material with specific places where electrons should be (like silicon), if an electron moves out of its designated spot, what’s left is called a hole. A hole effectively has a positive charge, and, as electrons move from hole to hole, it looks like the hole moves (even though, strictly speaking, it doesn’t – it just gets filled or emptied by a moving electron).
host
The main processing unit in a system. It controls how all other processors in the system operate. It’s the boss.
hub
A piece of electronic equipment that gathers separate related things together. A network hub, for instance, might bring together the individual network connections of multiple local users. A sensor hub brings together sensor data from multiple separate sensors for possible combination.
Or, more specifically, a device in the home (or elsewhere) that acts as a central point connecting a variety of smart-home (or other) devices. The devices talk to the hub; the hub talks to the cloud.
I/O
Stands for input/output. This refers to the signals that come into and depart from the computing system (as opposed to the signals running internal to the computing system).
idempotence
A property of a command or operation such that doing it once or more than once yields the same result.
IIoT
Industrial Internet of Things. A broad collection of factory, automotive, agricultural, medical, and other areas where IoT technology is used.
inertia
The tendency for an object to keep moving (or not moving) at a constant speed if you don’t accelerate or decelerate it. There’s inertia in a straight line and there’s also inertia of rotation – spinning things want to keep rotating in a specific direction unless you force them to change.
inertial measurement unit
A sensor that uses inertia to measure acceleration or deceleration either in a straight line or in rotation.
inertial measurement unit
A combination sensor with an accelerometer and a gyroscope, and, often, with a magnetometer. The first two rely on inertia to tell you where you are and where you’re going.
inference
For machine learning, this refers to the process of making decisions using a model. Before the decisions can be made accurately, training must occur.
infrared
Light below the frequency of (or with longer wavelength than) visible light. The wavelength range is roughly from 800 nm to 1 mm. Near infrared is the range near the visible part of the spectrum, from 800 nm to 2500 nm.
instruction set
Each processor or processor family has a specific set of instructions that it can execute. This is called the instruction set, or sometimes the instruction-set architecture (ISA).
insulator
A material through which electricity cannot readily flow. Plastic is a good, familiar example.
intellectual property
This can have lots of meanings, but, in the computer-chip world, it refers to parts of a chip design that have been built and optimized by one company, which then sells them to other companies that don’t want to design those blocks themselves. They’re not selling actual chips; they’re selling the design of a block that will be used within a chip.
interface
The point where two different domains meet, like a border. For example, a wall plug could be thought of as the interface between the power grid and the appliances you plug in.
interference
When two radio signals exist at the same frequency, you end up with a combination of both. They are then said to be interfering with each other, meaning that they mess each other up.
internet service provider
A communications company that provides internet access to homes, phones, or companies. For consumers, this could be the cable company, a phone company offering DSL, or a cellular service provider.
interoperability
This refers to how well different pieces of equipment can work together. Macs and PCs, for instance have some limited interop, but there are many Mac devices that can’t work on a PC, and vice versa. This is an important notion for systems, like the IoT, that involve many different pieces of equipment working together.
interrupt
A processor feature that let’s some event interrupt the program that a processor is running for a short time before returning the processor to the original program. In and IoT device, it may wake the processor rather than interrupting some other task.
IoT
The Internet of Things. A broad term covering many different applications where “things” are interconnected through the internet.
IP
This can mean two things (at least):
- The Internet Protocol. Governs the addresses of sources and destinations on a network (without worrying about what’s in between). Used on Layer 3 of the stack.
- “Intellectual property.” This can have lots of meanings, but, in the computer-chip world, it refers to parts of a chip design that have been built and optimized by one company, which then sells them to other companies that don’t want to design those blocks themselves. They’re not selling actual chips; they’re selling the design of a block that will be used within a chip.
IP address
An address used by the Internet Protocol (IP) to identify a machine on the network.
IPsec
A network-layer security protocol. Largely used between gateways for traffic traveling between (but not within) LANs. Not likely to be used within IoT devices.
ISM
A band of frequencies that anyone can use. In order to avoid interference, there are rules as to how one can broadcast on this band so that everyone plays nice together.
key
A number used to encrypt (or encode) information so that no one can read it. Keys are used when encoding and decoding. You shouldn’t have to mess with keys yourself.
LAN
A data-link-layer security protocol, largely used with Ethernet. This protects data within a LAN only. It’s normally administered by IT professionals. Not likely to be used within IoT devices.
latency
This can have various meanings, but in the context of a pipeline, it’s how long a specific single task takes to get be completed.
leakage
The very small amount of current that can flow through a transistor when it’s “off.”
legacy code
A collection of software that’s been built up over the years. It’s usually been improved an optimized gradually for the processor it’s running on, and it works, so developers will be reluctant to make major changes to it.
load balancing
A way of handling heavy server traffic by having multiple servers that can do exactly the same thing and then using another server as a dispatcher to assign tasks to the least busy servers.
machine
In our context, a machine is anything that isn’t human (or living). That includes electronic equipment like computers and phones.
machine code
The lowest-level representation of a computer program. It consists only of 1s and 0s, which a computer (or a machine) understands, but which is VERY hard for humans to understand.
machine language
This is the lowest-level representation of a program – the 1s and 0s that the processor sees and understands. It’s very hard for humans to read.
machine learning
Machine learning (or ML) is a process by which machines can be trained to perform tasks that required humans before. It’s based on analysis of lots of data, and it might affect how some IoT devices work.
machine vision
Technology that gives machines the ability to see things and make decisions based on what they see.
MACsec
A data-link-layer security protocol, largely used with Ethernet. This protects data within a LAN only. It’s normally administered by IT professionals. Not likely to be used within home IoT devices.
magnetometer
A sensor that detects magnetic fields — from the earth or from anywhere else.
malware
Software that usually finds its way into a computer or phone or IoT device without the knowledge or approval of the device’s owner. It’s malware when the intended purpose of the software is to cause some kind of harm.
master key
A security key used in some systems to create individual root keys for IoT devices.
matrix
An array of numbers, having both rows and columns of numbers. Widely used for many complex tasks.
memory address
When referring to memory, a binary number that shows where, within some memory block, the data you want is located. If you want to read or change that data, you have to give the address so that the right data is read or changed.
memory management unit
Circuitry that keeps track of what’s been loaded from a hard drive into DRAM and translates virtual addresses into physical addresses.
micro-services
Small programs that do things that, in an earlier time, would have been done within one large program. Breaking them out into smaller programs that then act as services to other programs makes them more robust and easier to maintain.
model
A simplified representation of something real. We can create models of things in our heads without even realizing we’re doing it. Technology often involves models because they let us simplify what would otherwise be extremely detailed, complicated concepts by focusing only on essential elements.
modem
A piece of network equipment that converts data into a format that can be transmitted. Old modems sent the data on a phone line; modern cable modems send the data across a cable connection. It stands for “modulator/demodulator.”
modulation
This generically refers to how some physical medium – like a wire or a radio signal – is modified to carry data. It might be by moving the voltage up and down, or it might be by changing frequencies of some periodic signal. There are lots of ways of “coding” data so that it can travel across the medium. It’s a really low-level detail; most of us don’t need to know any of the fine print. The opposite of modulation is demodulation, and a piece of network equipment that does both (modulation for sending, demodulation for receiving) is called a “modem.”
MQTT
A lightweight transport protocol for Layer 4; may be more appropriate for IoT equipment.
MQTT
A communications protocol designed for small systems such as those used for the IoT.
multi-tenanting
In the Cloud, this refers to a situation where multiple different users or systems are sharing the same server. Ideally, those different “tenants” will never affect each other.
multi-tenanting
When a cloud server is used to host more than one set of programs or users.
multicast
A means of sending a message to multiple specific destinations (unlike broadcast, which isn’t specific).
multicore
Describes a computer chip that has more than one CPU on it.
name server
A server that’s part of the internet infrastructure. Its job is to take a website name (like “InsideTheIoT.com” and return the IP address for that website. That lets us use human-friendly names that then get turned into machine-friendly addresses.
near-threshold
Circuits done where an active transistor works barely above the threshold voltage
net neutrality
The notion that an internet service provider needs to treat all traffic equally, without giving preferential treatment to traffic from specific companies.
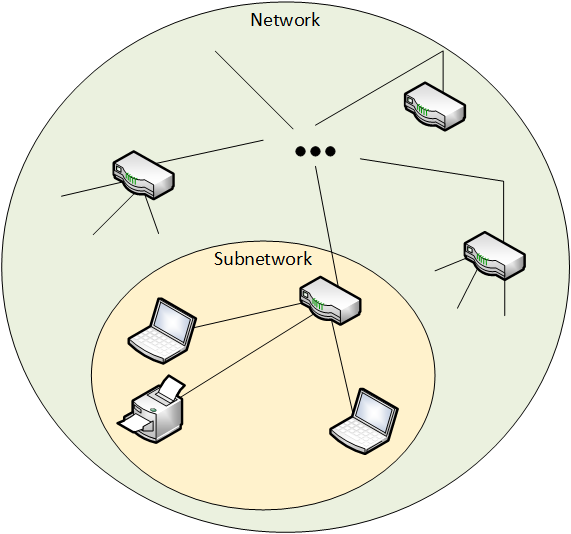
network
A collection of items like computers, printers, phones, and other electronic items that are connected together by switches and routers. A network allows the connected devices to talk to each other electronically. The internet is an example of an extremely large network. Your home network, if you have one, is an example of a small local network.
neural network
A type of conceptual network organized in a manner inspired by our evolving understanding of how the brain works.
neuromorphic
This refers to systems that attempt to operate in the same way that the brain operates. Spiking neural networks are the main commercial example.
non-blocking
In the context of a thread, refers to threads that can go off and do their thing without any other part of the program having to wait for them to finish.
object
When talking about programs, these are “things” that can be created in a way that encapsulates the details, letting them be accessed from outside through an interface.
object code
A program that’s been assembled, compiled, or translated into machine code.
object-oriented programming
A programming style where the programmer creates and manipulates objects to achieve a goal.
octal
A base-8 counting system (rather than the base-10 system we usually use). Digits can go from 0 to 7.
on-boarding
This is the process of connecting an IoT device for the first time. You connect to a network, and then the device connects “home” for registration and for confirming that the device is legitimate.
on-boarding
This is the process of connecting a new IoT device to the cloud for the first time. You have to get onto a local network first (maybe WiFi, maybe Bluetooth), and then you can reach the cloud.
operating system
Software – or firmware – that handles the low-level aspects of a computer or IoT device. It gets direct access to all the resources. Software asks the OS for access to those resources.
orientation
The direction someone or something is facing. This may be different from the direction of motion.
orthogonal
At right angles (or 90°) to something else. More generally, two settings or properties that you can set independently of each other are said to be orthogonal.
OTA update
A way of updating IoT devices by sending a new software package wirelessly to the device. But the concept is valid also for devices that aren’t updated wirelessly.
oxide
A substance created when oxygen binds to some other element. When that happens with iron, we get rust. When that happens with silicon, we get materials like sand and quartz. Often, the oxides of conductors and semiconductors will be insulators.
packet
A group of bits being sent from one place to another. How big the group is may vary depending on what kind of packet it is. Long messages — like an email — will typically be broken up into many packets, each of which travels independently until it gets to the destination, where they’re reassembled into the email.
page
A chunk of memory on a hard drive or SSD that can be brought into DRAM for use or for execution.
payload
The main contents of a message. Using an analogy, when you receive a letter in the mail, the letter itself is the payload; the envelope is merely a carrier.
periodic
This can be a characteristic of some signal. If the signal changes somehow, and that change repeats itself exactly over time, over and over – like a sine wave – then the signal is said to be periodic. The amount of time it takes for the signal to repeat itself is called the “period.”
periodic
An event that repeats itself over and over again at some fixed rate or frequency.
photolithography
A way of creating patterns on a silicon wafer for selective deposition or etching. You can think of it as taking a picture of the pattern and having it show up on the wafer. In the industry, photolithography is often abbreviated as lithography.
photomask
A piece of glass with a pattern on it that is used to block light or let light pass through in different places. Used for photolithography.
physical address
The location of some item in physical memory.
piezoelectricity
A natural phenomenon with certain materials where, if you stress them mechanically (bend, for example), they exhibit an electrical change. The reverse also occurs: if you apply an electric field, they will bend or deform in some way. The effect is tiny, but measurable.
pipeline
A way of speeding up a repeated task by breaking it up into stages and having different resources do each stage. It takes longer for the first task to be completed (that’s the latency); the others come out in quick succession after the first one.
plasma
A fourth state of matter (the other three being solid, liquid, and gas). It’s characterized by atoms being stripped of their electrons; it takes a lot of energy to get into this state.
platform
This word can mean different things. It may mean a set of infrastructure on which someone can build an IoT device or service. Or it could be a generic piece of hardware that can be used for many different things.
pointer
A variable that, instead of holding data, holds an address where data is located. That is, it “points” to the data instead of being the data.
polling
Refers to a processor that’s looking for something to happen, and it simply asks over and over and over again whether it’s happened until it does happen.
power
The rate of energy consumption. For electricity, it’s measured in watts (W).
printed circuit board
Some kind of board (usually rigid) that gets metal connections “printed” onto it. Electronic components can then be soldered on.
privacy
Refers to whether or not information gathered about your usage of IoT devices by authorized people can be made public, or shared with others, without your consent. Different from (although related to) security, which protects such data and devices from access by unauthorized people. Different from privacy, which is more concerned about use of data by authorized people.
private key
A key that should be known only by your device and, possibly, by someone or something else that your device is communicating with. It must be kept secret.
private key
A key that must be kept secret or else security will be blown.
processor
A computer chip that does computing work for a computer. It may do general work (like in your home computer) or it may do specialized work (like some of the processors in your smartphone).
profile
An agreed-upon definition of how some device works – what commands it can receive – and what those commands should look like.
protocol
An agreed way of doing something. Like a convention, except that protocols tend to be related to processes.
provisioning
This is a manufacturing step where your IoT device gets its own private key. The key and your device’s ID are likely stored in a database so that your device can be recognized when you connect for the first time.
pseudonymize
To take data that has personally identifiable information and separate out or obscure the link between the data and the individual. The link can still be made, so it’s not anonymous, but it’s harder to make the link.
public key
A key that you (or your device) can publicly share with someone or something else. This key can be used only to encode (or encrypt) data; it can’t be used to read that data. Each public key has a matching private key, and the private key is used for decoding (or decrypting) data. This lets you have a secure conversation with someone or something that you’ve never shared keys with before.
public key
A key that can be freely sent out in public, without being hidden. It works because it’s paired with a separate private key that’s needed for reading a message that was encrypted with the related public key.
public/private key infrastructure
A system of mathematical algorithms for public and private keys as well as certificates of authority that are used when authenticating a web session.
publish-and-subscribe
A way of sending data to multiple destinations. The destinations subscribe to the data using a broker; whatever is generating the data (possibly a sensor) publishes the data to the broker; the broker either sends to the data to the subscribers or lets the subscribers request data.
real time
This is a term that refers to computing or other processing that happens at the same speed as something is actually happening. A familiar example might be spell-check in your word processing program. In the old days, you did a spell-check of the entire document after it was written. Modern programs do spell-check “in real time” – that is, right as you type, it’s checking; no waiting until the end and doing the whole document at once. Doing something in real time is often a good thing, but it means you have to do whatever you’re doing fast enough to keep up.
real-time operating system
An OS where various tasks can be guaranteed to be completed within a specific timeframe.
recognition
In the context of machine vision, a task that identifies not just what kind of thing is in the image, but which specific individual it is.
rectification
The process of eliminating or transforming the negative parts of an AC signal or power.
request/response
One way machines can communicate, where one machine sends a request (or issues a command) to another machine; that other machine responds with data or maybe with an acknowledgment to a command.
resistance
Forces that tend to reduce the amount of flow or current. Measured in ohms (Ω).
REST
A way of programming that has evolved out of web programming, and it’s more abstract than other older languages like C.
RISC
Reduced Instruction Set Computer; a kind of processor that has far fewer instructions than a CISC processor. It can still do the same things, but it may require the use of multiple simpler instructions instead of one complicated instruction.
RNN
A type of artificial neural network used for analyzing streaming input like speech or handwriting.
rollback
When talking about software updates, this refers to a situation where a new update fails and you want to revert to the old version.
root key
A key that is typically unique to each IoT device (but might not be) and which is used to create session keys for communication between IoT devices and IoT servers in the cloud.
router
An electronic box that helps steer data on a network. For instance, you may have one in your home connecting your phone and computer and other devices to each other and to the internet. The data itself has information about where it’s being sent; the router uses that information to send it in the right direction. At a really basic level, you can think of a router and a switch as being the same thing. If you want to get more technical, a switch creates a local subnetwork, and the router connects multiple subnetworks (or multiple networks).
security
Refers to whether or not IoT devices or data are protected from unauthorized viewers.
semiconductor
A material that, under some circumstances, can conduct electricity and, in other circumstances, cannot.
sensor
A device that can measure something about its environment. Examples are movement, light, color, moisture, pressure, and many more.
sensor fusion
The process of combining information from multiple sensors (real or virtual) in order either to give more confidence in a result or to come up with something completely new.
server
A computer with a dedicated purpose. Older familiar examples are print servers (a computer that controls local printing) and file servers (a computer used for storing files centrally). More modern examples are web servers (the computers that handle your web requests when you use your browser) or application servers (computers dedicated to handling the computing needs of a specific application). Servers are often powerful, expensive machines since they have to handle a heavy load.
services
We are used to purchasing products outright. “Services” is a new concept where you may or may not buy the product, but optional or mandatory services come with the product. Those services may have an ongoing cost separate from the purchase price.
session key
A one-time-use security key used for encryption during a single communication session between an IoT device and an IoT server.
silicon
An element (number 14 in the periodic table) that can be a semiconductor, making it the material of preference for circuits and micro-mechanical devices.
sleep
The state of a machine where as many non-essential electronic elements as possible are shut down, without powering the machine completely down.
smart city
A general name for cities that use technology to make things work better for residents, workers, and visitors.
smart home
A buzzword for interconnected home devices – TV, refrigerator, door locks, etc.
software
In this context, “software” refers to functions in an IoT device that are implemented by running instructions through some kind of processor. It’s distinct from “hardware,” where functions are built into a silicon chip or some other component.
source code
A program that’s readable by a human, usually in a high-level language.
spectrometer
An analysis tool that measures how something responds to different frequencies (or colors) of light. Those colors might not be visible to humans – like infrared or ultraviolet.
spectrum
A range of frequencies. A prism shows a range, or spectrum, of visible light frequencies (yes, light is a wave). This is the literal definition of spectrum. Other uses – like references to the autism spectrum use the word figuratively to indicate a continuous range. In our context, this refers to the range of radio frequencies available for communication. Access to those frequencies is usually regulated by governments since they’re viewed as a public asset.
speculation
Done by a processor, it means that the processor has to guess ahead of time what the result of a test will be so that it can load those instructions into the pipeline. If it’s wrong, it will have to empty the pipeline and restart with the correct instructions.
spiking neural network
An approach to neuromorphic machine learning that attempts to mimic how the brain (or parts of the brain) works.
SRAM
Stands for “static random access memory.” This is also temporary memory in a computer. It’s very fast compared to other kinds of memory, but it’s also very expensive and burns a lot of energy, so you don’t have nearly so much.
SSD
A memory that acts like a hard drive, but is built out of flash memory instead.
SSL
Secure Sockets Layer. A common internet security protocol. TLS is a more recent version of this, but SSL is still used. Works with TCP on Layer 4 of the stack.
stack
Related to communications: A way of organizing parts of a complicated process (like communications) so that any task relies on tasks below it and feeds the tasks above it.
Related to computing: A place in memory where you store “where was I?” information when you go from, say, one function into another. Before starting a new function, you store where you were in the old one so that, when the new function ends and you’re back in the old one, you can figure out where you were and continue on.
stall
Ideally, a CPU executes instruction after instruction, with no breaks. But there are times when there may be a delay – getting new data from DRAM or having to reload the pipeline due to a branch, for example. When this happens, we say that the system briefly “stalled.”
standard
A way of doing something specific that has been agreed by multiple parties in an official manner. Some “standards” aren’t official standards; the best ones have been established in an open fashion, where anyone with an interest can contribute and where large companies can’t push little companies around.
standards body
A group of companies getting together in a manner consistent with anti-trust laws to agree on how to do things. Rather than limiting competition, this is intended to foster competition by getting agreement on some basic thing (like wall sockets having 110 V) and then letting companies compete on that basis.
state
A broad term that can apply to a lot of systems. Let’s say you have a system that can be one of two ways – on or off. That “on-ness” or “off-ness” is the state of the system. The system is either in an on state or an off state. Many different kinds of systems can have many different kinds of state. There are many complex branches of engineering or physics or even mathematics that deal with state. The easiest way to think of any of them is, “the way things are” (which may depend on the history of prior states, meaning how they got to this particular state).
static power
The rate of energy consumption of a circuit when nothing is switching — it’s just sitting idle.
storage
This usually refers to memory that doesn’t lose its contents when powered off – like a thumb drive or a hard disk. It’s a place to store data.
sub-threshold
Circuits done where an active transistor works below the threshold voltage.
subnetwork
A portion of a bigger network. For example, if you have a home network and it’s connected to the internet, then your home network is a part of the overall internet network. That home part is therefore a subnetwork. Any self-contained subset of a bigger network can be called a subnetwork.
subroutine
A small portion of a program that’s set aside and given a name. It helps isolate key code in an easy-to-understand way, and it makes changes easier and less error prone. It’s a really important way to make programs easier to understand. May also be called a function.
super-threshold
Circuits done where an active transistor works at voltages well above the threshold voltage
supercapacitor
A type of capacitor that can be used for storing energy.
supervised learning
A machine learning approach where a machine is trained by giving it examples and, during the training, telling the machine what the answers are. A large number of varied examples provide the best results.
switch
A switch helps direct network traffic to the right destination. At a high level, it’s very similar to a router. Technically, switches are used to create local subnetworks; routers connect subnetworks together.
symmetric key
A way of encrypting data that uses the same key both for encrypting and decrypting.
system
This is a very generic term for any collection of components that, all together, can do something. Systems can be built from subsystems. Examples are your cell phone; your computer; the radio in your car; anything that seems like a “whole.”
system of systems
A system built out of other smaller systems. Just as you might say that a system could be built out of subsystems, you can also say that separate systems can be combined to create a larger system. They’re just different ways of saying the same thing.
TCP
Transmission Control Protocol. A more reliable way to set up connections that might have two-way traffic or need better guarantees that messages get delivered. Used on Layer 4 of the stack.
TCP/IP
Pronounced “TCPIP” or “TCP over IP.” A common configuration where TCP is used on Layer 4 and IP is used on Layer 3.
telemetry
Measuring information about communications. For the IoT, it could be things like how and when things are communicated, how much is communicated, etc.
the cloud
A generic phrase referring to large numbers of computers located somewhere far away and accessed over the internet. For the IoT, computing may be local, done in the same system or building, or in the cloud, with data shipped up to the cloud and then the result shipped back down.
the fog
Refers to some way of doing “cloud”-style computing without having to use the cloud. A local server (or router or something else) can act like the cloud; because it’s local, it’s referred to informally as the fog.
thermometer
A sensor that measures temperature.
thread
A piece of a program that can execute at the same time that some other piece of that same program can execute.
threshold voltage
The voltage at which a transistor starts to turn on. It’s technically “off” below that voltage, although it is still ever so slightly on.
TLS
Transport Layer Security. A very common internet security protocol. You can think of it as an updated version of SSL, although both are still used. Used with TCP on Layer 4 of the stack.
traffic
Refers to any kind of electronic message — email, web
training
With machine learning, a model must be trained in order to perform its function (which is called inference).
transducer
A device that converts one kind of energy, like the energy of motion, into another, like the energy of an electric current. Transducers are fundamental to sensors, since they let us measure something physical as an electric current.
trusted execution environment
A separate area inside a processor where trusted software can run, with access to all resources. Software running outside that area has to access resources through the trusted area; it can’t do so directly.
tunneling
A phenomenon where current can flow through a very thin insulator due to quantum effects.
UDP
User Datagram Protocol. A “best effort” (i.e., no guarantees) way to get a message from one place to another. Used on Layer 4 of the stack.
unicast
Sending a message to one single destination.
Unicode
The modern way of representing worldwide characters in computers. It covers all existing scripts and then some. It replaced ASCII.
unsupervised learning
A machine learning approach where a machine is trained by learning as it goes. It doesn’t get trained by examples ahead of time, and isn’t explicitly taught the “right answers.” There must be some other way of reinforcing the right and wrong answers as it learns.
user interface
This is an interface between something and the user of that thing. In a car, the pedals and steering wheel are all part of the user interface. You’re probably more familiar with the user interface (or UI) on a computer. If that interface involves graphics, then it’s a graphic user interface, or GUI (pronounced “gooey”).
vector
A one-row matrix that can have any number of columns.
virtual
In our context, refers to what are usually software models of some physical thing. The model behaves like the real thing except, in some cases, in performance.
virtual address
The location of some item as generated by a compiler. In more complex systems, it will likely need to be translated to a physical address by an MMU before it can be used.
virtual machine
A way of configuring a portion of a real-world computer to look and act like a complete computer on its own. The idea is to have multiple virtual machines on a single real machine.
virtual memory
A scheme for translating virtual addresses, created by a compiler, into the physical addresses representing where things are located in a real system.
virtual sensor
A source of data that, strictly speaking, isn’t a sensor, but that can be used as if it were a sensor.
voltage
Voltage is what gets electrons to flow. It’s analogous to water pressure, which gets water to flow. Voltage is measured in units of “volts.”
wafer
In the context of making circuits, sensors, and actuators, a thin, round slice of pure silicon. Multiple devices will be made on it; it will then be sliced up to separate the individual chips.
wake word
For personal assistants like the Amazon Echo, this is a word or phrase that the device listens for. When it hears it, it knows (or thinks) that you’re going to give it a command.
walled garden
An approach to the IoT that restricts which devices and brands you can have work together. It could protect you, help assure interoperability, keep out certain competitors, or any and all of the above.
WAN
Wide-area network. This is a broad description of the core networks that connect different LANs together around the world. When traffic leaves a building, it usually goes through a gateway out onto the WAN before returning elsewhere through a different gateway into a different LAN. You could think of this as the internet.
web server
A server whose purpose is to receive requests for web pages and then send those pages out to the requestor.
WiFi
A common type of wireless network used to connect computers and phones to each other and the internet.
wireless power
Technology that allows a battery to be charged from a small or large distance, over the air, without having to connect a charger.
word line
A line in a memory that selects which word (and its associated bit cells) will be selected for reading or writing, based on the memory address. The word lines and bit lines are orthogonal to each other, making an array of the bit cells that connect them.